Juniper Management Routing Instances
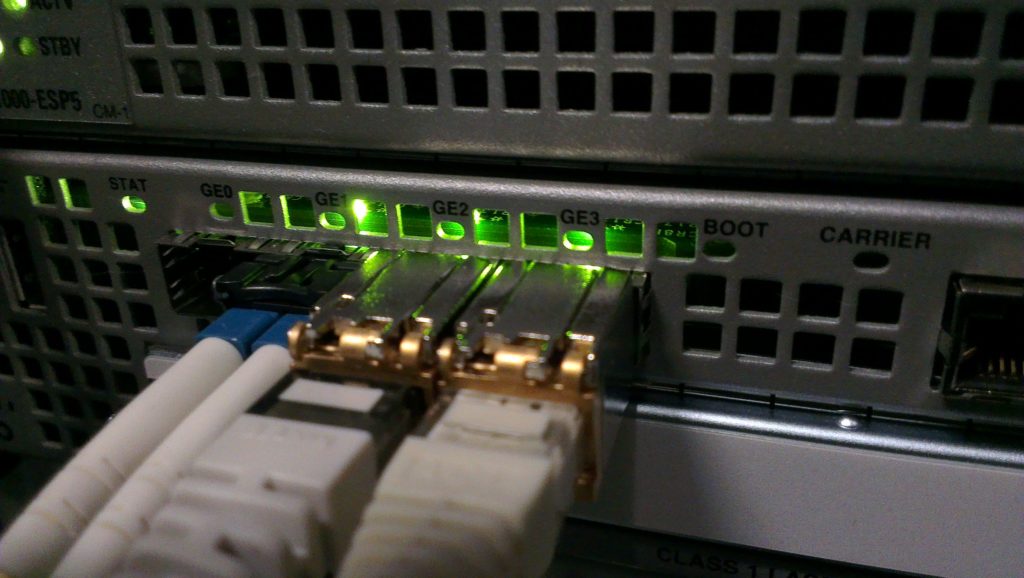
If you’re doing network security properly, you are running the management interfaces of your network devices – (routers, switches, server management boards) – on a completely separate network from your end user traffic, so that management traffic is maintained out-of-bounds (OOB).

OOB networks achieve several things – it separates management traffic, through which login credentials may be passed – from operational network traffic, providing a layer of security. Administrative access to the device should not be available from any other network to which the device is connected.
Secondly, OOB networks can provide a non-flooded network path to the device if the operational interfaces of the device are under some kind of attack – (eg: DDoS) – increasing your chance of getting onto the device to take remedial action without having to take the device completely offline.
So, pretty useful.
I’m currently working on a firewall deployment and found myself needing to configure the management interfaces on a pair of Juniper firewalls. It used to be difficult to connect the management interface to the network without using the same routing table as the operational traffic.
Yes it could be separate, but you weren’t able to get the management interface – (typically “fxp0”) – into its own virtual routing instance so that it could be physically connected to a different physical network, while still being routed. This would be required when you’re not on the same network as the device, and you have to get to it remotely.
I’ve achieved this in the past, but it’s been a super long time since I’ve had to do it, so had to go Googling to remind myself what you had to do. The Juniper document has all the pieces required, but smooshed it all up in other discussion and for some people it will be hard to follow.
It only requires three commands and JunOS 17.3R1 and above to achieve – (you have been doing updates, right?)
Let’s say your management network is 192.168.11.0/24, with a default gateway of 192.168.11.254.
The first thing you need to do is tell the device that you want to use a management virtual routing instance. This is a special kind of virtual routing instance that works slightly differently than any others you might need to run on the device.
Just turn the feature on with the following:
set system management-instanceThis tells the device to enable a routing instance specifically for the management interface, which for most Juniper devices is “fxp0”.
Next, set the address you want within your network range, for example “192.168.11.11”, noting that it needs to be on the management interface – (noting the “fxp0” reference):
set interfaces fxp0 unit 0 family inet address 192.168.11.11/24Then you need to create the special routing instance to tie it all together. This routing instance must be called “mgmt_junos” – (when you enable management-instance with the first command, it tells JunOS to look for a routing instance with that name, so that it knows to treat it as management traffic only, and therefore prevents you from creating two of them) – and then set the default route on that management network:
set routing-instances mgmt_junos routing-options static route 0.0.0.0/0 next-hop 192.168.11.254Done.
The device will now route traffic within your management network, independently of the routing table for the rest of the traffic – thereby separating the management traffic from anywhere the bad guys might be hitting you from!