Sunday Nerding: The Clock That Changed The World
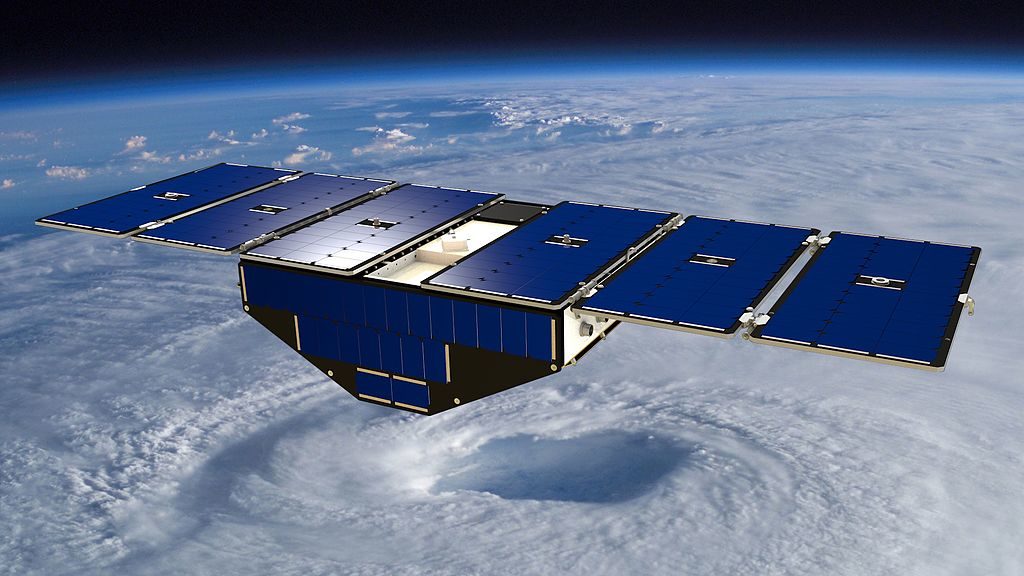
Before there was GPS, people still needed to sail the oceans of the world and know precisely where they were.
With a sextent, you could figure out your latitude, but not your longtitude. Enter the Longitude Rewards, a British government program to encourage someone – anyone – to find a accurate way to determine longitude.
Enter John Harrison, and his incredibly accurate clock.